Introduction
Have you ever wondered how secure your business is against cyber threats? In today's digital landscape, cybersecurity is no longer an option but a necessity. With cyberattacks increasing in frequency and sophistication, businesses of all sizes must implement robust security measures to protect sensitive data, maintain customer trust, and ensure business continuity. According to recent statistics, global cybercrime is expected to cost businesses $10.5 trillion annually by 2025, making cybersecurity one of the most critical investments for any organization.
True Value Infosoft, a top IT company in India, has been at the forefront of providing cutting-edge cybersecurity solutions tailored to businesses' needs. With a strong track record of delivering highly secure software solutions, cloud security services, and threat intelligence systems, True Value Infosoft has helped businesses across industries safeguard their digital assets. The company’s commitment to cyber resilience and compliance with international security standards makes it a trusted partner for organizations looking to fortify their cybersecurity framework.
What is Machine Learning?
Machine Learning (ML) is a subset of Artificial Intelligence (AI) that enables computers to learn and make decisions without explicit programming. ML uses data, statistical algorithms, and pattern recognition to improve decision-making and predictive capabilities.
In cybersecurity, ML plays a crucial role by analyzing vast amounts of data, detecting anomalies, and identifying potential security threats. It helps organizations predict and prevent cyber attacks before they occur by recognizing patterns in previous security breaches. Common applications of ML in cybersecurity include:
- Threat detection and analysis
- Spam filtering
- Fraud detection
- Behavioral analytics to identify suspicious activities
What is Cybersecurity?
Cybersecurity refers to the practice of protecting computer systems, networks, and data from cyber threats, unauthorized access, and attacks. It encompasses a wide range of security measures, including encryption, firewalls, antivirus programs, multi-factor authentication (MFA), and security policies.
Cybersecurity involves several key aspects:
- Network Security: Protects data transmitted over networks from unauthorized access and cyberattacks.
- Application Security: Ensures software and applications are secure from vulnerabilities.
- Information Security: Protects sensitive business and customer data from breaches.
- Cloud Security: Secures cloud-based systems and data against cyber threats.
- Endpoint Security: Protects end-user devices like laptops, smartphones, and IoT devices from cyber risks.
The Role of Cybersecurity in IT
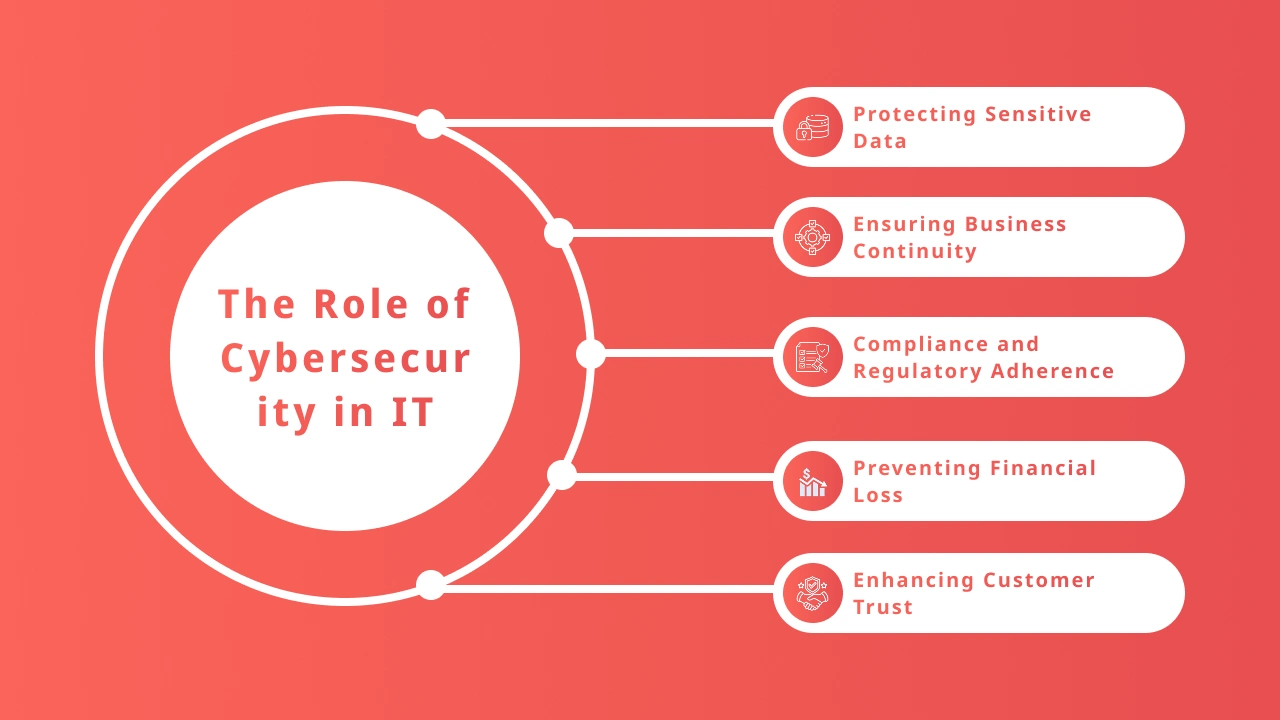
The IT industry heavily depends on cybersecurity to protect critical data, maintain system integrity, and ensure smooth business operations. The key roles cybersecurity plays in IT include:
- Protecting Sensitive Data: Ensures customer information, financial records, and proprietary business data are secure from breaches.
- Ensuring Business Continuity: Prevents downtime caused by cyberattacks, keeping business operations running smoothly.
- Compliance and Regulatory Adherence: Many industries have strict regulations (e.g., GDPR, HIPAA, PCI-DSS) that require businesses to implement strong cybersecurity measures.
- Preventing Financial Loss: Cyber attacks can result in substantial financial losses due to fraud, theft, and downtime.
- Enhancing Customer Trust: Secure systems build customer confidence and loyalty, ensuring they feel safe using a company’s services.
Major Cyber Threats in the IT Field

Cyber threats have become more sophisticated over time, targeting businesses of all sizes. Here are some of the most critical cyber threats faced by organizations today:
- Phishing Attacks: Fraudulent emails or messages designed to trick users into revealing sensitive information such as login credentials or financial details.
- Ransomware: Malicious software that encrypts files and demands a ransom for their release.
- Distributed Denial-of-Service (DDoS) Attacks: Overloading a system or network with excessive traffic to disrupt operations.
- Malware and Viruses: Malicious programs that infect systems, steal data, or cause damage.
- Insider Threats: Employees or business partners who misuse access privileges to compromise company security.
- Zero-Day Exploits: Attacks targeting previously unknown software vulnerabilities before they can be patched.
- SQL Injection: Hackers exploit vulnerabilities in databases to gain unauthorized access to information.
- Man-in-the-Middle (MitM) Attacks: Cybercriminals intercept and manipulate communication between two parties.
Importance of Cybersecurity in the IT Field
The significance of cybersecurity cannot be overstated. Without proper security measures, businesses face the risk of data breaches, financial loss, reputational damage, and legal consequences. Some key reasons why cybersecurity is essential include:
- Prevents Data Breaches: Protects business and customer data from unauthorized access.
- Safeguards Financial Assets: Reduces the risk of financial fraud and theft.
- Protects Intellectual Property: Ensures proprietary information remains confidential.
- Regulatory Compliance: Avoids legal repercussions and hefty fines by adhering to industry standards.
- Strengthens Brand Reputation: Demonstrates a commitment to security, building trust with customers and partners.
Why True Value Infosoft is the Best Choice for Cybersecurity
True Value Infosoft stands out as a leader in cybersecurity solutions, offering cutting-edge security services to protect businesses from cyber threats. Here’s why True Value Infosoft is the best choice:
- Comprehensive Security Solutions: Offers a full suite of cybersecurity services, including network security, endpoint protection, and cloud security.
- AI-Driven Threat Detection: Utilizes advanced AI and machine learning to detect and prevent cyber threats in real-time.
- Customizable Security Frameworks: Tailors cybersecurity solutions based on the specific needs of businesses.
- 24/7 Monitoring & Incident Response: Provides round-the-clock security monitoring and rapid incident response to mitigate threats.
- Regulatory Compliance Expertise: Helps businesses adhere to cybersecurity regulations and industry standards.
- Trusted by Leading Businesses: Proven track record of securing enterprises across various industries.
Case Study: Cybersecurity Implementation for a Financial Institution
Background
A mid-sized financial institution faced increasing cyber threats, including phishing attacks and attempted data breaches. They required a robust cybersecurity solution to protect sensitive customer data and ensure compliance with industry regulations.
Challenges
- Frequent phishing attacks targeting employees.
- Risk of financial fraud due to weak authentication mechanisms.
- Compliance requirements (e.g., PCI-DSS, GDPR) needed to be met.
- Lack of real-time threat monitoring.
Solution by True Value Infosoft
True Value Infosoft implemented a multi-layered cybersecurity approach, including:
- AI-Powered Threat Detection: Deployed AI-based security solutions to detect and prevent phishing and malware attacks.
- Multi-Factor Authentication (MFA): Strengthened access controls to prevent unauthorized logins.
- Real-Time Security Monitoring: Set up 24/7 security monitoring to detect and mitigate threats instantly.
- Employee Cybersecurity Training: Educated staff on best practices to recognize and avoid cyber threats.
Results
- 85% Reduction in phishing attack success rates.
- Zero Data Breaches since implementation.
- Full Compliance with industry security standards.
- Increased Customer Trust, leading to higher retention rates.
Conclusion
Cybersecurity is a critical aspect of modern business operations, protecting companies from cyber threats, financial loss, and reputational damage. Implementing strong cybersecurity measures ensures data security, business continuity, and regulatory compliance. True Value Infosoft provides top-tier cybersecurity solutions, making it the ideal partner for businesses seeking reliable protection against cyber threats. By adopting proactive security measures, businesses can stay ahead of cybercriminals and safeguard their future in the digital world.
FAQs
AI enhances cybersecurity by detecting and responding to threats in real time, analyzing vast amounts of data for anomalies, automating routine security tasks, and predicting potential vulnerabilities before they are exploited. AI-driven security systems can quickly identify patterns and stop attacks before they cause damage.
AI can help defend against phishing attacks, malware, ransomware, insider threats, and advanced persistent threats (APTs). AI-driven tools can also detect zero-day vulnerabilities and automate responses to mitigate the risks posed by evolving cyber threats.
Businesses should integrate AI-driven threat detection, use machine learning-based behavioral analytics, automate incident response, continuously update AI security models, and combine AI with human expertise for a layered security approach. Regular employee training on cybersecurity best practices is also essential.
Yes, while AI enhances security, it also presents risks such as adversarial attacks, where hackers manipulate AI models, and over-reliance on automation, which may lead to blind spots. Businesses must continuously refine AI models, conduct audits, and use human oversight to ensure AI-driven security remains effective.
Many affordable AI-powered cybersecurity tools, such as cloud-based security platforms and managed security services, cater to small businesses. Leveraging AI-driven security in endpoint protection, intrusion detection, and email filtering can provide strong protection without a large IT budget.